Portals El Paso, TX (915) 217-2500 | Grapevine, TX (817) 752-9400
One Culprit Behind Last Week’s Massive Cyberattack? Weak Passwords
One Culprit Behind Last Week’s Massive Cyberattack? Weak Passwords
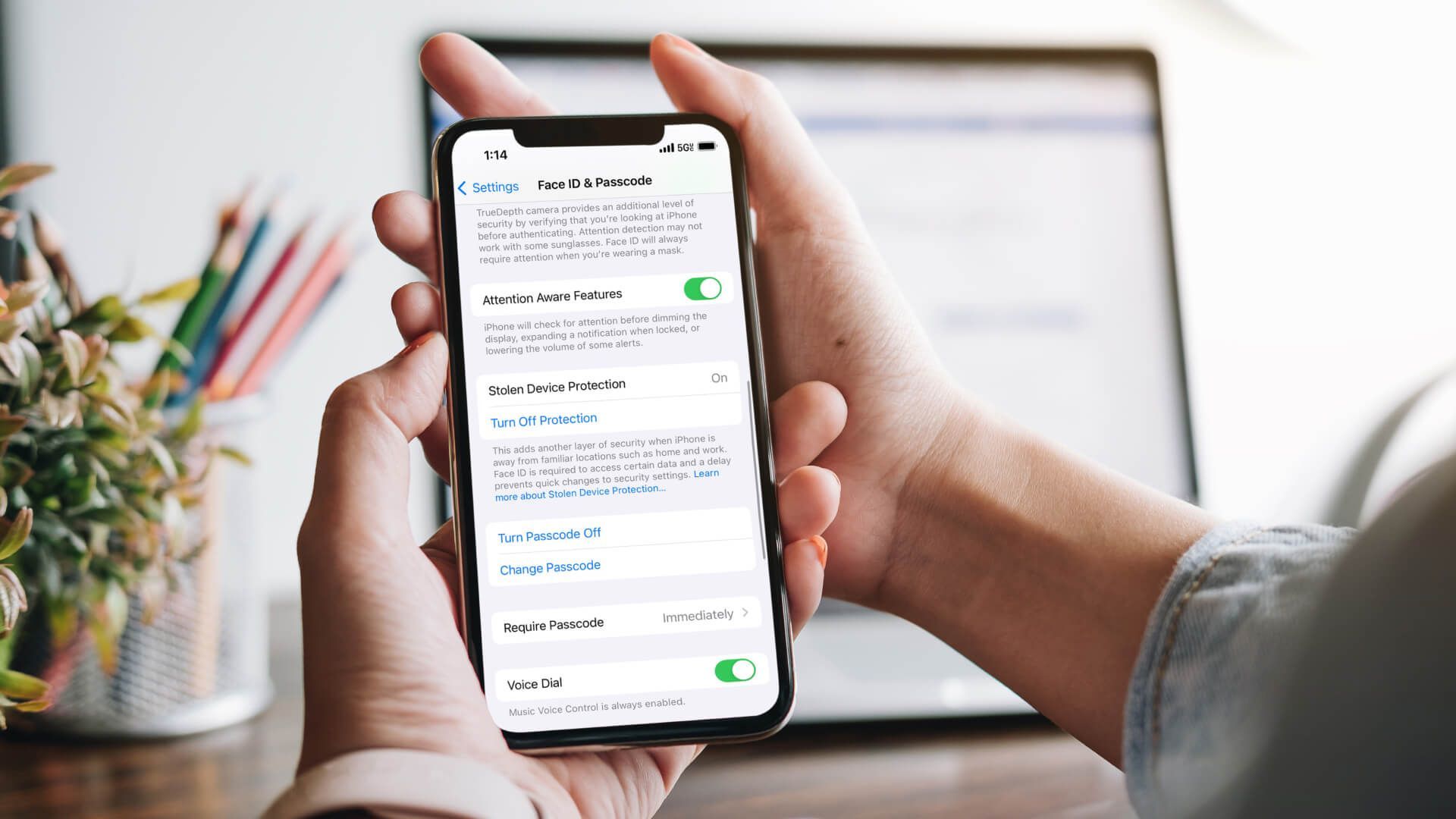
It’s that time again—your regular Password Health Check-up is due.
Now, before your eyes start to ‘roll and scroll’, skipping on to something you haven’t heard before, listen to this–
Last week’s massive cyberattack, which outsmarted some of the best and brightest and shut down major sites like Amazon, Netflix, and Twitter for hours, equaling losses in the millions?
One of the culprits behind it all–weak passwords.
If you haven’t had time yet to read about the attack and how it all went down (literally), here’s a helpful analogy for the non-geek, via tech blogger QuHarrison Terry–
‘Imagine Dyn [the DNS provider that was attacked] is the US Postal Service. If someone wanted to shut down USPS, they would get thousands of people to stand outside of every post office, each holding thousands of pieces of mail. They would continue this for days upon days until mail begins collecting in piles ten-feet tall all over the post office. Eventually, the workers get too stressed from overwork and just quit and the USPS mail system would cease existence.’
In this case, the thousands of people at the post office were millions of ‘smart devices’ like DVRs and cameras (part of the world’s massive and growing ‘Internet of Things’ (IoT), these are physical items that are ‘internetworked’ across the information society we all know and use every day).
So how were hackers able to use (actually, ‘enslave’) these gadgets and gizmos, some of which you may have in your home or office, to bring Dyn to its knees with thousands of 10-feet tall piles of requests (to go back to our analogy outside the post office)?
Simple. The devices were easy to hack and infect with malware because they were set with weak passwords.
Many of the products used were made in China by Hangzhou Xiongmai Technology, which said on Sunday that their products have weak default passwords that are easy to infect. As of Sunday, Mirai (the malware used in the attack) had been found spreading to at least 500,000 devices.
Okay so, once again, here’s Password Safety 101. First off, as astronomer Clifford Stoll has taught us,
To expand just a little on that–
- Never give out your password to anyone, even friends. Even a good friend may accidentally pass it along to others (or become an ex-friend).
- Don’t use the same one for everything. If one of the sites you use it on is compromised, it will be easier for someone to break into your accounts elsewhere.
- Create passwords that are easy to remember but hard for others to guess. Try using a short sentence or phrase and add some numbers. Or use only the first letter of each word of the phrase (i.e. “I went to Franklin Middle School in 1990” = “IwtFMSi#1990”). And make them at least a little different (by adding a couple of unique letters) for each site. On some sites you might even be able to type in the entire phrase.
- Short passwords are easy to hack, so always make the password at least 8 characters long. The longer the better.
- Include numbers, capital letters and symbols. Consider using a $ instead of an S or a 1 instead of an L, or including an & or %.
- Don’t use dictionary words. If it’s in the dictionary, it is guessable and hackable; especially by software designed to do just that.
- Don’t post your password in plain sight. This might seem obvious but studies have found that a lot of people post their password on their monitor with a sticky note. Bad idea. If you must write it down, hide the note somewhere where no one can find it.
You may also like
Have more questions or need further assistance? Let us know how we can help you with the unique needs of your business. Get in touch online or call us today at (915) 217-2500!
Cybersecurity for Businesses
Services
Management
Consulting
Cyber Security
Email Services
Cloud Internet
VoIP & Internet
Microsoft 365
Hardware & Software
Finance & Leasing
Websites & SEO
Industries
Healthcare
Engineering
Transportation
Construction
Insurance
Legal
Financial
Real Estate
Logistics
Manufacturing
About
Newsletters
Stewardship
Partners
News
Certifications
People
Employment
History
Clients
Company
Copyright © 2006-2023 All Rights Reserved. MAKIOS® is a registered trademark of Makios Group LLC, a Texas Company.