Portals El Paso, TX (915) 217-2500 | Grapevine, TX (817) 752-9400
What are Bots? Are they Safe?
What are Bots? Are they Safe?
Bots. If you’ve been surfing the web long enough, you have in one way or another ran into, interacted with, or have been subjected to bots, even if you weren’t aware of it. In this article you will learn all about bots – the good and the ugly, how they work, and how to work against them.
What are Good Bots?
An Internet robot, or a bot for short, is an automatic software system that provides services to users. These services are usually simple, repetitive tasks conducted so that human users don’t have to. Because they are automated, bots work at mimicking human behavior but at a quicker and more efficient rate, are available 24/7, and can reduce labor costs for organizations. Some useful functions of bots could include indexing search engines, customer service, and entertainment. Although bots could be used for good, they could also be used for bad. We will first explore how good bots work, some examples of good bots, and then flip the switch to explore bad bots – disguised malware that infiltrates and infects your device.
How do Good Bots work?
Bots are a composition of algorithms intended to carry out their designed task. Bots typically work by operating over a network, communicating with each other through internet-based services.
Types of Bots
Chances are, you have experienced the workings of bots. As mentioned, there are many different uses for bots. Here are a handful of some commonly used ones:
- Chatbots: Work in having a human conversation with human users.
- Intellectually Independent Chatbot: uses code to understand and learn from human inputs, remembers, and identifies common keywords to tailor their next question for the user.
- Rule-based Chatbot: communicates with users by asking pre-written prompts.
- Artificial Intelligent (AI) Chatbots: are a combination of Intellectually Independent and Rule-Based Chatbots. AI Chatbots uses natural language generation tools to mimic the rhetoric of human users.
- Scraper bots: These bots read and save data from a visited webpage for the purpose of reuse. This could be scrapping the webpage’s data as a whole, or scrapping specific data such as names, prices, and items.
- Social bots: are bots that work in social media platforms. These bots create a human-like persona, generating messages, act as followers of users via fake accounts, and gain followers. These bots are oftentimes created to influence discourse and ideas.
- Shop bots: are bots that work in observing a user’s shopping pattern and website navigation to customize results for the best price of the product the user is shopping for.
- Spider bots: or sometimes called web crawlers, scan and download HTML, JavaScript, and other resources off webpages across the internet to better equip Google and other search engines to best answer questions users ask.
Common Examples of Bots You May Recognize
These are a few ways in which bots may appear in your everyday usage of the internet on your device:
- News app outlets: work to showcase tailored news headlines for the user, such as The Wall Street Journal.
- Mastercard: grants access to users to check their account transactions by using the Facebook Messenger bot.
- Instant messenger apps: such as Facebook Messenger and WhatsApp.
- National Geographic: programed a conversation app to converse like Albert Einstein would have.
- Spotify: allowing users to listen to and share music over other apps, such as Instagram and Facebook Messenger.
What are Bad Bots?
Bots are a tool that are programed for a specific purpose. Thus, just as there are bots created for user efficiency, there are bots created to carry out harmful tasks towards users and their data. Today, 66 percent of bots are used in malicious ways. Bad bots are responsible for a large number of severe security threats to individual users, businesses, and organizations. Cybercriminals use malicious bots to steal personal and financial information, extort money from victims, attack legitimate network or web services and shut them down, or to extort money from other botnet systems.
How do Bad Bots Work? Botnets.
Malware that infects the user’s device oftentimes does so with the motive of enlisting the device into a botnet, or bot network. Once a device is infected, it begins to communicate within a Command and Control (C&C) center that is under the attacker’s control. Once a device is infected and enlisted to the C&C center, the attacker can then perform automated activities.
A goal for these attackers is to create a massive botnet system, spamming millions of computers and devices. This creates a botnet; a net of bot-infected devices to be controlled in malicious ways. After a while, attacker activity is not necessary, in that botnets could grow themselves by sending spam bots via email, and through social bots via social media to other devices to infect even more users.
Some capabilities of malicious bots include relay spam, collecting passwords, gathering financial information, opening and exploiting back doors on the infected computer, and insinuate DDoS attacks.
Botnet attack: Distributed Denial-of-Service (DDoS)
Distributed denial-of-service (DDoS) are the most frequent type of botnet attacks. A DDoS attack is an attempt to make a network or server resource inaccessible to users. This is done by the botnet’s accumulation of malware that saturates the device, causing a momentary suspension.
Serious successful cases of DDoS attacks may result in temporary loss of business, cause significant overcharges for providers, effect business reputation, and could even compromise the business’s data.
Other Common Malware Bot Tactics
One of the most common ways that bad bots infect your device is through download. Below we will explain a few different tactics that malware has used to entice users to fall victim to bad bots.
- File-sharing bots: These bots work at tricking the user by answering the user’s query with a downloadable link. If the user clicks, downloads, and opens the link, the malware infiltrates and infects the device.
- Malicious chatterbots: These bots work to emulate human conversation via dating websites to persuade the user that they are a real person. The objective is to extract personal information from the user, including credit card information.
- Spambots: These bots collect email addresses from social media, websites, and businesses. After a large number of emails are collected, emails are then paired with common passwords to gain unauthorized access. Spambots can also automatically insert spam in websites such as advertisements and malware links.
How to tell if you are a Victim of Bad Bots.
Bad bots could be hard to spot. They usually nestle in the darkest corners of your computer to avoid detection. However, being aware of the small signs of infiltration could help to bring the bad bots to the surface. To tell if your computer has been enlisted in a botnet, keep an eye out for:
Slow and obscure device activity. This includes:
- Your device crashing without reason.
- Your device does not shut down properly or takes a very long time to shut down.
- Internet access slows drastically or stops working.
- The fan on the device goes into overdrive even when not using the device.
- You cannot download system updates.
- Settings change without the ability to change them back.
Spam activity. This includes:
- The high velocity of pop-up windows and advertisements when not using the web browser.
- Your contacts receive emails from you that you did not send.
- Your browser has downloaded items that you did not download yourself.
What to do if you are a Victim of Bad Bots.
If some of the above tell-tale signs are happening to you and your device, chances are that you have fallen victim to bad bots. The most important thing to do if this happens is to save your data! Immediately disconnect your device from the network to cut the theft activity. Then quickly move all your personal data to an external hard drive or another device that is malware-free. You will then need to deep clean your device. This can be done with assorted security tools. However, you may need to have a professional work on the device in extreme cases.
Stay Protected! Preventing Bad Bots.
Now that you have awareness of good and bad bots, their tactics, and their effects on your device, you are one step closer in keeping your device protected from bots! Here are a few more recommendations to keep the bad bots at bay.
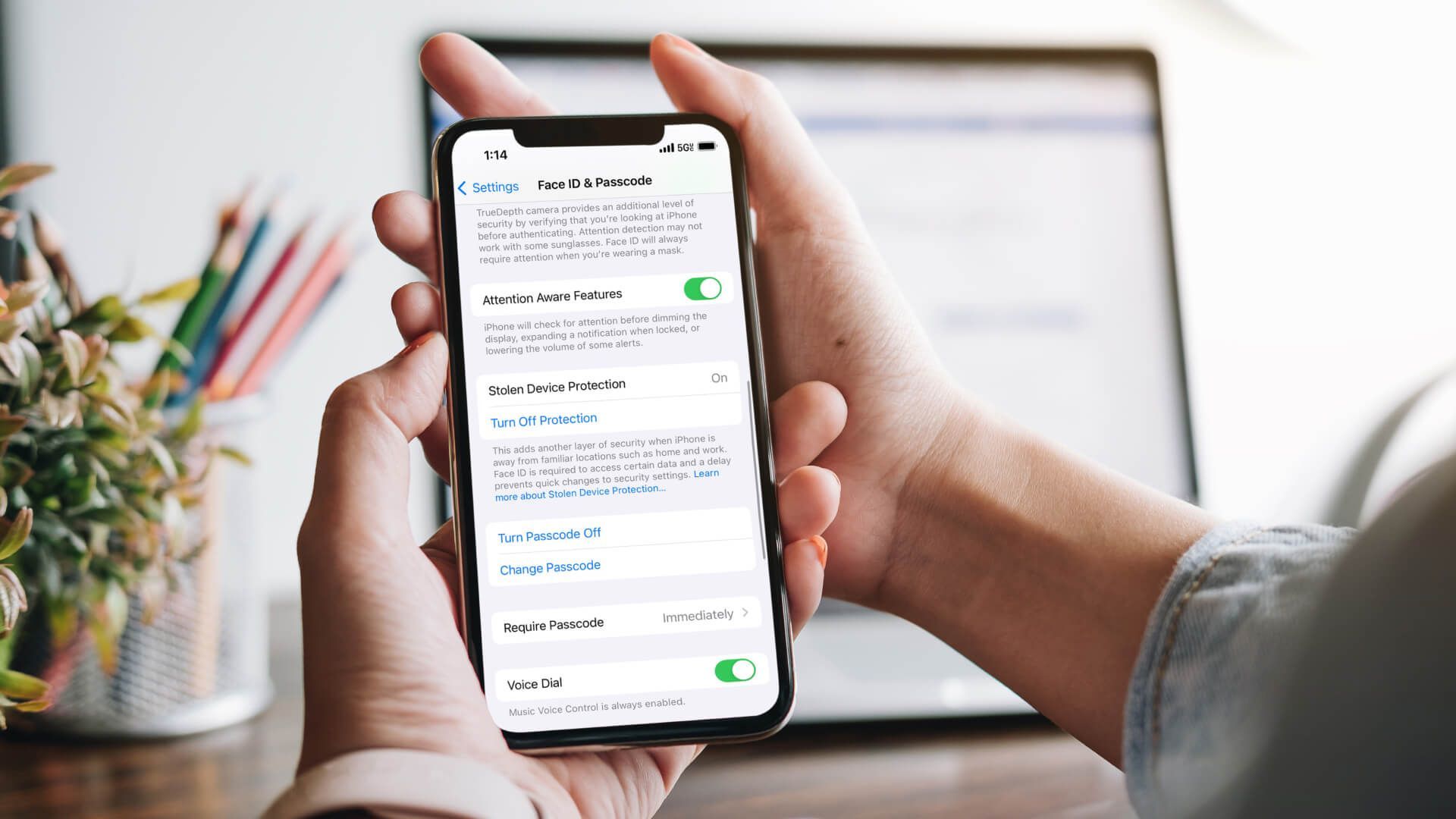
- Invest and install quality anti-malware software.
- Install firewalls to prevent infiltration of bad bot attacks.
- Keep your device’s software up to date.
- Do not use the same password for various programs.
- Make your passwords lengthy and complicated, complete with numbers, letters, and symbols.
The reality is that bots, good and bad, are everywhere. They either help by making our experiences as device users more efficient or maliciously crash our device completely. Thus, it is important to be knowledgeable about the bots working right under our noses. Remember, a good defense is a good offense! Stay in control of your device and your data from getting hijacked by practicing good prevention skills and staying alert of signs of infection. Professional quality managed cybersecurity services from Makios Technology will do a lot of good for your security online.
Learn more about how we can keep you protected. Give us a call today at (915) 217-2500 or take a moment to complete our online contact form.
You may also like
Have more questions or need further assistance? Let us know how we can help you with the unique needs of your business. Get in touch online or call us today at (915) 217-2500!
Cybersecurity for Businesses
Services
Management
Consulting
Cyber Security
Email Services
Cloud Internet
VoIP & Internet
Microsoft 365
Hardware & Software
Finance & Leasing
Websites & SEO
Industries
Healthcare
Engineering
Transportation
Construction
Insurance
Legal
Financial
Real Estate
Logistics
Manufacturing
About
Newsletters
Stewardship
Partners
News
Certifications
People
Employment
History
Clients
Company
Copyright © 2006-2023 All Rights Reserved. MAKIOS® is a registered trademark of Makios Group LLC, a Texas Company.