Portals El Paso, TX (915) 217-2500 | Grapevine, TX (817) 752-9400
10 Best Practices to Protect Your Employees' Mobile Devices
10 Best Practices to Protect Your Employees' Mobile Devices
With the rise of mobile technology and remote work, the security of employees' mobile devices has become more critical than ever. Ensuring that sensitive data remains protected is a top priority for businesses. In this blog post, we will explore 10 best practices on how to secure your employees' mobile devices, from establishing strong user authentication to monitoring and preventing mobile application threats.
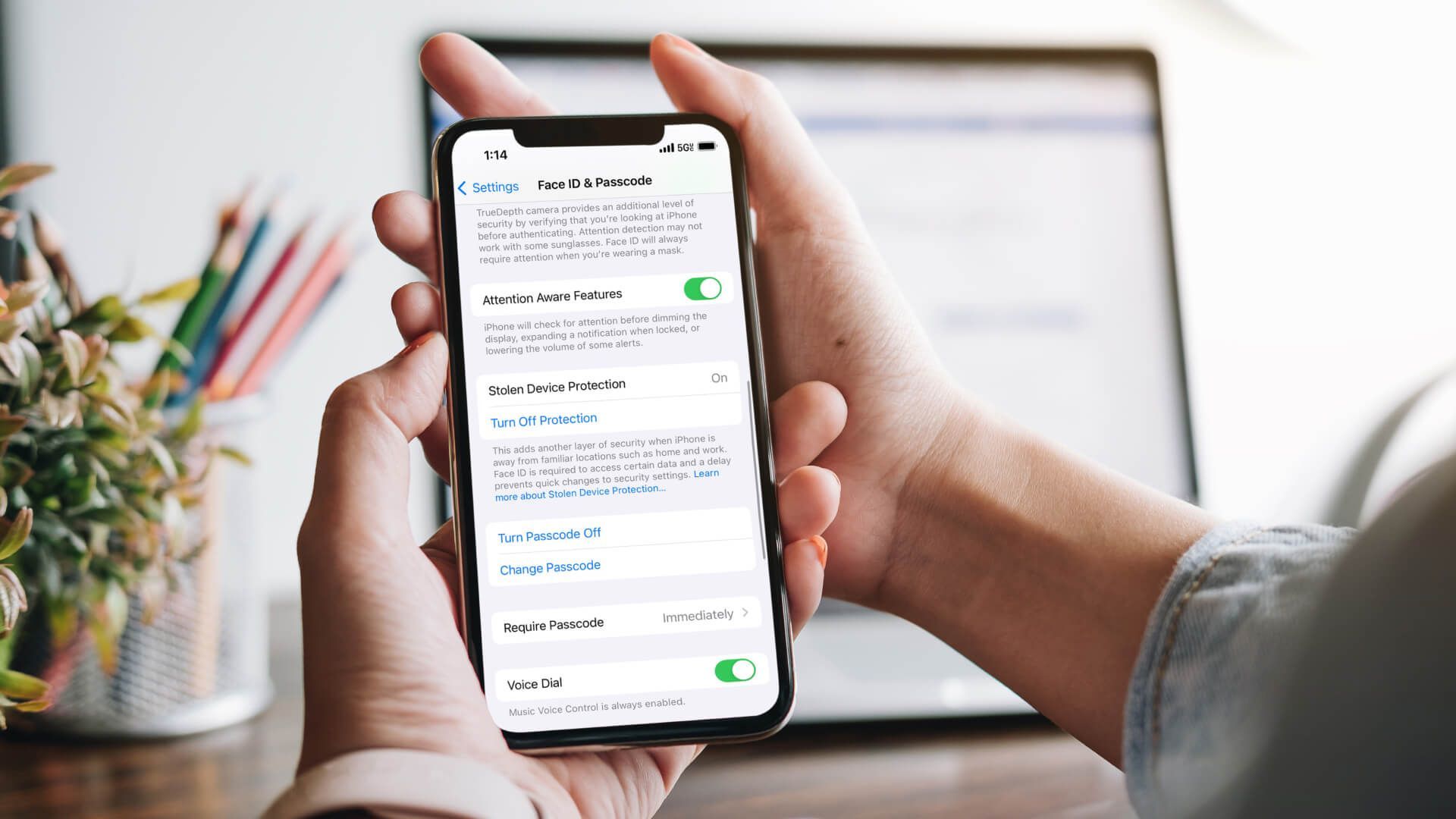
1. Establishing Strong User Authentication
Strong user authentication is essential to safeguard sensitive data stored on mobile devices and restrict unauthorized personnel from accessing them. The three user authentication methods on mobile phones are screen lock, password or PIN, and biometrics. Password security policies, such as password expiration every 60 to 90 days and setting character length and combination requirements, play a crucial role in enhancing mobile device security in the workplace.
In addition to these measures,
Multi-Factor Authentication (MFA) offers an extra layer of security that necessitates more than one authentication method. This method can help defend against data breaches and unauthorized access to confidential data, especially when using mobile device management.
2. Utilizing Password Management Tools
A password manager is a tool that securely stores all your passwords in a single, protected location, with access granted only via a master password. These tools store passwords and generate strong, unique passwords that can help protect users from using weak passwords and reduce security vulnerabilities.
Employees can better comply with password security policies and protect sensitive and corporate data by employing a password manager. Combining a password manager with an MFA app can further optimize mobile security protocols.
3. Regular Operating System and App Updates
Regularly updating operating systems and applications reduces potential security risks and ensures optimal protection. Without the necessary security measures in place, such as anti-ransomware and anti-malware software, businesses are at an increased risk of sophisticated ransomware and malware attacks that can cause significant damage.
Maintaining current operating system configurations is essential to ensure the most robust security measures are in place. Aso, consider using alternative authentication methods, such as SSH keys, which can provide additional security for server access.
4. Steering Clear of Public Wi-Fi Networks
Unsecured devices connected to public Wi-Fi networks are vulnerable to exploitation by hackers. Sensitive business data could be compromised if employees access work accounts on unsecured public Wi-Fi.
A Virtual Private Network (VPN) can establish a secure connection between the company network and a mobile device, safeguarding all communications transacted through an open Wi-Fi network and encrypting communications when personnel are in a foreign country or working remotely.
Before logging in through an unsecured public Wi-Fi network, employees should utilize a VPN to ensure their data remains protected.
5. Ensuring Cloud Security and Data Backup
Cloud security and data backup are essential to guarantee that data remains accessible in the event of a lost or stolen device. Implementing a cloud-to-cloud backup solution effectively protects against the permanent loss of deleted files or earlier versions. Several cloud platforms, such as Google's G Suite, Microsoft Office 365, and Dropbox, offer version history of files.
When implementing cloud backups, it is essential to implement appropriate encryption practices to mitigate potential risks and maintain data security.
6. Leveraging Mobile Device Management (MDM) and Mobile Application Management (MAM) Solutions
Mobile Device Management (MDM) provides the capability to monitor, manage, and configure the devices utilized by employees remotely, including laptops, mobile devices, and tablets. Mobile Application Management allows IT personnel to control and analyze application usage on personal devices. It also allows them to configure installed apps remotely. Integrating MDM and MAM can create robust security measures, blocking unauthorized devices from accessing a company's network of applications and data.
An MDM is the most effective solution for remotely tracking and erasing a phone without access to the employee's Google or Apple account. Utilizing automatic deployment with an MDM system can offer additional benefits, such as enforcing secure lock codes on employee mobile devices and tracking phones without relying on third-party tools like iCloud.
7. Encouraging Encryption Practices
Encryption is essential for safeguarding data stored on and transmitted to and from mobile devices. Transmitting personal and sensitive information over public Wi-Fi networks can expose users to risks such as inadequate end-to-end encryption, Man-in-the-Middle attacks, data alteration in transit, and eavesdropping. Encryption policies guarantee that confidential data is not stored on unencrypted or personal mobile devices. Users can encrypt data before storing it on their device, which is essential in the event of a lost or stolen device.
By encouraging employees to use encryption for data protection on their mobile devices, businesses can prevent sharing sensitive information over unsecured networks and reduce the risk of security breaches.
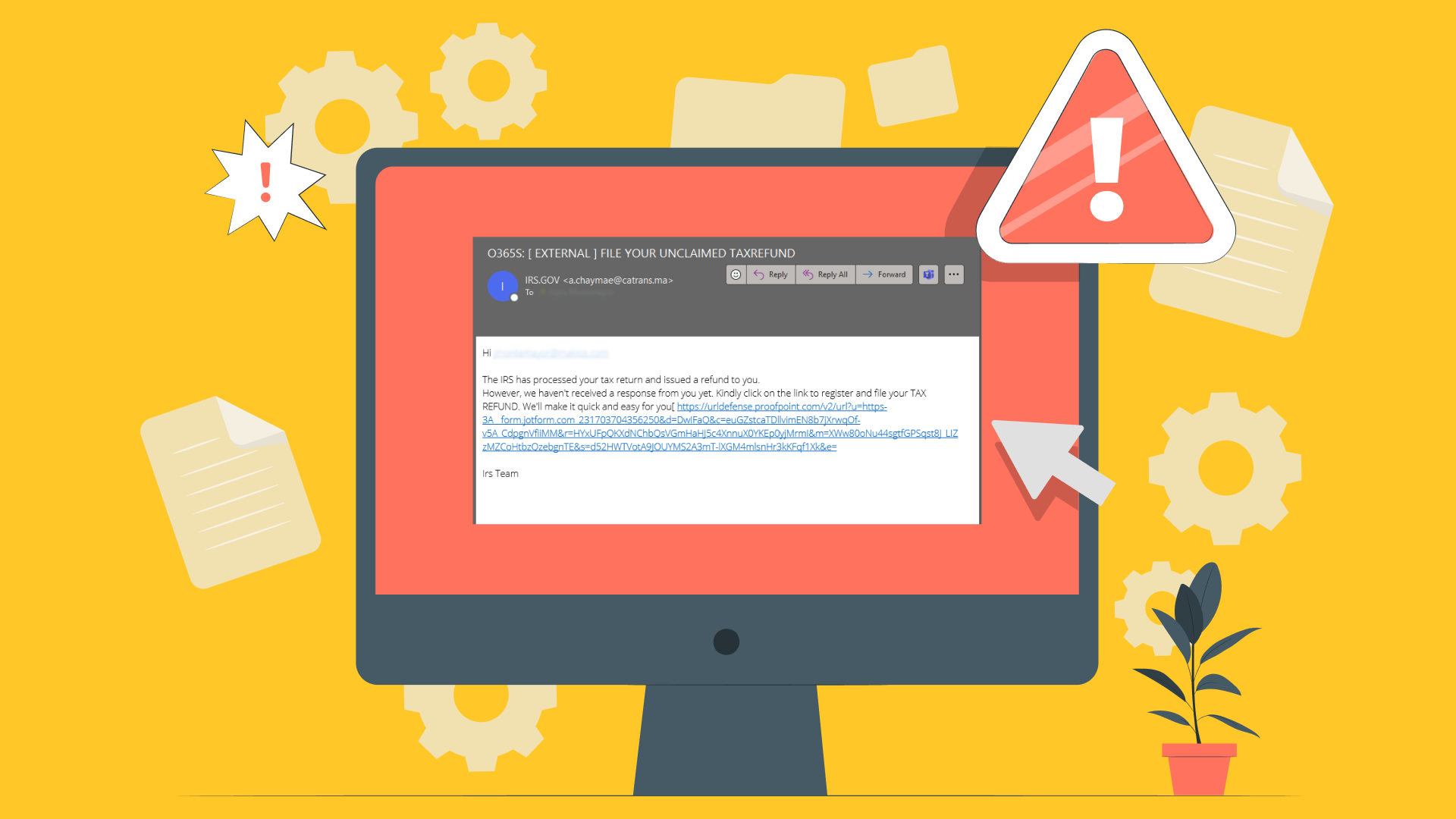
8. Educating Employees on Phishing Scams
Phishing attempts to illicitly obtain confidential information, such as passwords and credit card numbers. Phishing scams are a common way to try and steal your details, potentially leading to a security breach. They can come as an email or instant message with a link or an attachment that may contain malware. The ramifications of succumbing to a phishing scam could include disclosing data on the dark web, account takeover attempts, and ransom demands.
Employees should exercise caution when encountering such messages and consider their options thoughtfully before responding to protect themselves from phishing scams.
9. Practicing Caution with App Permissions
Phishing attempts to illicitly obtain confidential information, such as passwords and credit card numbers. Phishing scams are a common way to try and steal your details, potentially leading to a security breach. They can come as an email or instant message with a link or an attachment that may contain malware. The ramifications of succumbing to a phishing scam could include disclosing data on the dark web, account takeover attempts, and ransom demands.
Employees should exercise caution when encountering such messages and consider their options thoughtfully before responding to protect themselves from phishing scams.
10. Communicating and Enforcing Mobile Device Security Policies
Disseminating mobile device security best practices is essential to inform stakeholders about potential threats and the recommended measures to reduce mobile device security risks. User training is critical for mobile device security due to the potential impacts of theft or misuse, such as a breach of the corporate network, the loss or corruption of necessary data, and the violation of industry compliance regulations.
Fostering an environment of recognizing the dangers posed by cyberattacks to an organization is essential. Users must comprehend and comply with the policy for it to be effective.
Take Control of Mobile Device Security with Makios Technology
In conclusion, mobile device security is of utmost importance in today's increasingly connected world. By following these 10 best practices, businesses can minimize the risk of security breaches and protect sensitive data on employees' mobile devices. From establishing strong user authentication to monitoring and preventing mobile application threats, it's essential to be proactive in securing your organization's mobile devices and ensuring the safety of your valuable data.
Here at Makios, we’ll help you find the solution that meets your organization's needs and safeguards your digital assets against ever-evolving cyber threats. Contact us today!
You may also like
Have more questions or need further assistance? Let us know how we can help you with the unique needs of your business. Get in touch online or call us today at (915) 217-2500!
Cybersecurity for Businesses
Services
Management
Consulting
Cyber Security
Email Services
Cloud Internet
VoIP & Internet
Microsoft 365
Hardware & Software
Finance & Leasing
Websites & SEO
Industries
Healthcare
Engineering
Transportation
Construction
Insurance
Legal
Financial
Real Estate
Logistics
Manufacturing
About
Newsletters
Stewardship
Partners
News
Certifications
People
Employment
History
Clients
Company
Copyright © 2006-2023 All Rights Reserved. MAKIOS® is a registered trademark of Makios Group LLC, a Texas Company.