Portals El Paso, TX (915) 217-2500 | Grapevine, TX (817) 752-9400
Comprehensive Guide to MFA/2FA & Microsoft Authentication
Comprehensive Guide to MFA/2FA & Microsoft Authentication
As a cybersecurity specialist, I know first-hand that there is no perfect, fail-proof solution to cybersecurity problems. The cyberattacks on major supply lines and industries such as the Colonial Pipeline and JBS show that we exist in the digital cold war, with the battles happening minute-by-minute in cyberspace.
However, there are practical steps that businesses and individuals can take to ensure that their personal data and information are protected to the highest possible degree. In fact, many cybersecurity issues can be solved, and hacks prevented by taking simple authentication steps.
One question I often receive is, “What is the best security method for my data?” When it comes to protecting your personal data on devices and cloud-based software, there are two powerful methods that offer protection: two-factor authentication (2FA) and multi-factor authentication (MFA).
To fully comprehend the two authentication options, let us delve deeper into each of them and analyze the advantages of Microsoft Authentication as a viable solution for authentication.
What Are Authentication Factors?
Authentication Factors act as a digital “identity check” for someone trying to access protected data, services, resources or information. Authentication Factors are identified by three “types”:
Knowledge: Something you know, such as your own username, password or PIN code.
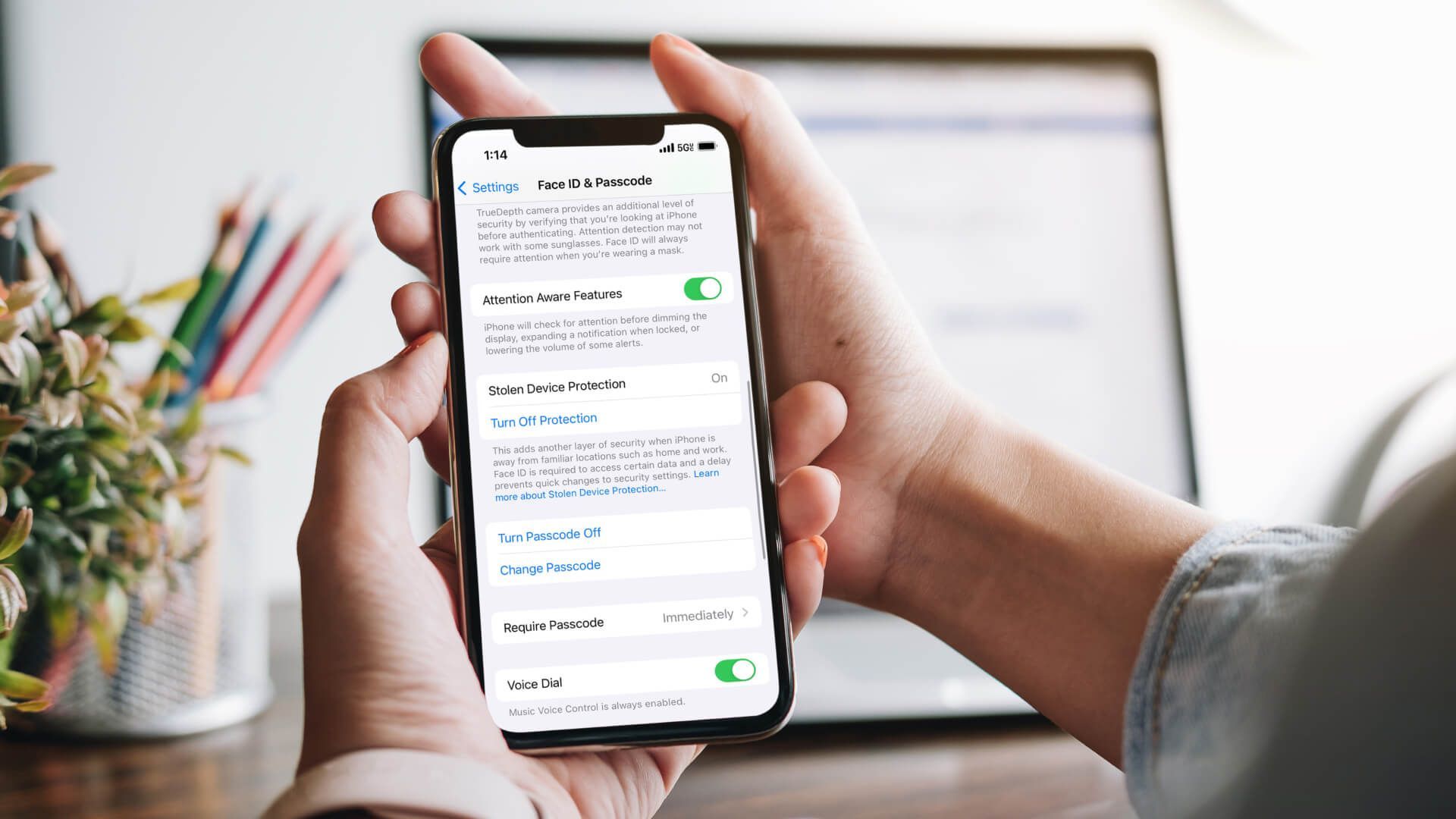
Possession: Something you prove you have, like a cellphone, key fob, or USB drive with two-factor authentication software installed on it. This is known as “something you have” authentication because this device acts as a backup or an extra form of ID.
Inherence: Something you are, such as a fingerprint or retina scan. This is known as “something you are” authentication because this identification method requires your physical presence and can be done in person on a mobile device with biometrics technology installed.
Most users of digital technology have grown accustomed to single-factor authentication, such as a password to unlock one’s online bank account. However, sign in others, if only one piece of information – such as a “knowledge” password – is required, then the risk is much higher that more options than that single factor could fall into the wrong hands.
To increase your protection, I always encourage individuals to invest in 2-factor or multi-factor authentication methods.
What is 2-Factor Authentication?
Two-factor authentication is a method of identification in which two out of three factors have to be used, and they are always the same.
For example, if someone has your password or username (something you know) and physical access to your mobile phone (something you have), that person or organization would also need something else – such as an email or text message – to access your account.
What is Multi-Factor Authentication?
Multi-factor authentication requires the use of three or more different factors as a type of identification. It often includes something you have, such as a USB drive with two-factor software installed on it (something you possess), in addition to knowledge and one other form of verification.
One of the most popular forms of multi-factor authentication is a software app that you can download to your computer or mobile device and install. Known as “something you have” because this type of two-factor authentication requires a physical item, these types of apps are straightforward to set up and use. In fact, they generally require no more than a few taps.
Which Type Offers the Most Protection?
Multi-factor authentication is more secure because the third factor can be anything – from a fingerprint to an email address. Therefore, sign in again. If someone has your password and physical access to your phone but doesn’t know about any of the other factors you have set up for two-factor authentication (such as logging in with your thumbprint), that person would not be able to access your account.
So, when it comes to protecting your personal data on devices and cloud-based software apps and services – which one is more secure?
For maximum security, I recommend going with multi-factor authentication for all of your user accounts where possible. If you cannot do this (for example, if you’re a small business owner who needs to log in as an office administrator but can’t access your thumbprint), I would recommend going with two-factor authentication for multiple accounts when possible.
As with anything else, the more layers of protection you can build around your personal data, the safer you will be. While one or two layers may fall to a sophisticated hacker, that third inherence layer may stand firm and keep your data from being stolen.
What is Microsoft Authentication?
Microsoft Authentication, also referred to as Azure Multi-Factor Authentication, is a widely adopted implementation of multi-factor authentication (MFA). It is a robust security solution provided by Microsoft, designed to bolster the security of user accounts and safeguard sensitive data. By enforcing the requirement of additional authentication factors beyond a simple username and password, it adds an extra layer of protection.
How to Use the Microsoft Authenticator App
One of the convenient ways to implement multi-factor authentication with Microsoft is by using the Microsoft Authenticator app. The app is available for download on various platforms, including iOS and Android devices.
Here are the steps to set up and use the Microsoft Authenticator app for multi-factor authentication:
- Login to your Microsoft 365 account on your computer and click on your profile photo in the top right corner.
- Select “View account”
- Click "Update Info" under the Security Info section.
- On the Security info screen, you will find your default sign-in method displayed, along with a list of all the methods currently linked to your account. To register the Authenticator App, choose the "Add sign-in method" option.
- To add an authenticator app, select "Authenticator app" from the dropdown menu and click the "Add" button.
- Download the Microsoft Authenticator app from your device's app store.
- Click Next until you get a QR code.
- On your mobile device click “Add account”
- Choose the work or school account.
- Accept requested permissions and notifications.
- Use your mobile device to scan the QR code from your computer.
- Click “Next”
- After scanning, you will get a code on your computer to add to your Authenticator app.
- To make it the default sign-in option, select “Change” on your Security info screen.
- Choose Microsoft Authenticator - notification, then Confirm.
Isn't MFA Inconvenient?
While it’s true that MFA (and 2FA, at that) require more steps to unlock trusted device or gain access to the location of your data, it is important to remember what you are protecting.
If you are worried about your data, then I would argue that the inconvenience of logging in is worth it. Do you know what would be the greatest inconvenience? Discovering that terabytes of your most valuable data have been compromised or stolen. Even worse – the data of someone else being taken and held for ransom.
Trust me. There is nothing worse than that moment you have to negotiate with ransomware hackers for millions – if not billions – of dollars to retrieve your company data.
Protect Your Data with Makios Cloud MFA
Hackers and malicious entities online are getting more sophisticated by the day. If you aren’t taking steps to protect your data now, you can guarantee you or your organization will fall victim to a cyberattack soon.
You wouldn’t leave your front door wide open while your family sleeps at night – so don’t forget to let your business data face the same risks.
If you are looking for a way to keep your online accounts, passwords and business data secure with the latest security, we can help you with our Makios Cloud MFA service.
Contact us to get your business started with Makios Cloud MFA.
You may also like
Have more questions or need further assistance? Let us know how we can help you with the unique needs of your business. Get in touch online or call us today at (915) 217-2500!
Cybersecurity for Businesses
Services
Management
Consulting
Cyber Security
Email Services
Cloud Internet
VoIP & Internet
Microsoft 365
Hardware & Software
Finance & Leasing
Websites & SEO
Industries
Healthcare
Engineering
Transportation
Construction
Insurance
Legal
Financial
Real Estate
Logistics
Manufacturing
About
Newsletters
Stewardship
Partners
News
Certifications
People
Employment
History
Clients
Company
Copyright © 2006-2023 All Rights Reserved. MAKIOS® is a registered trademark of Makios Group LLC, a Texas Company.